To top

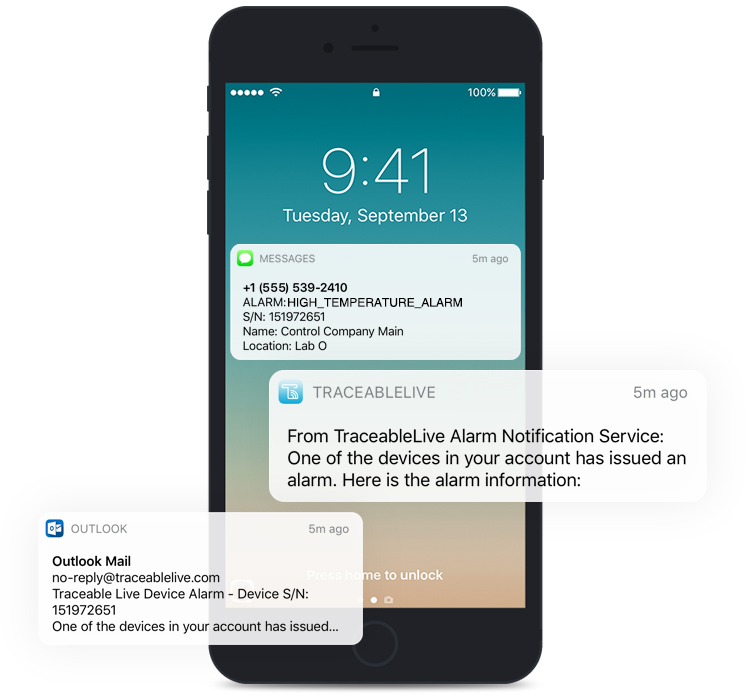
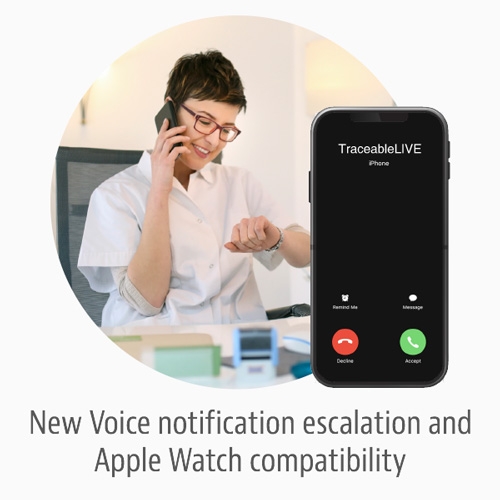
Get notified wherever you are—

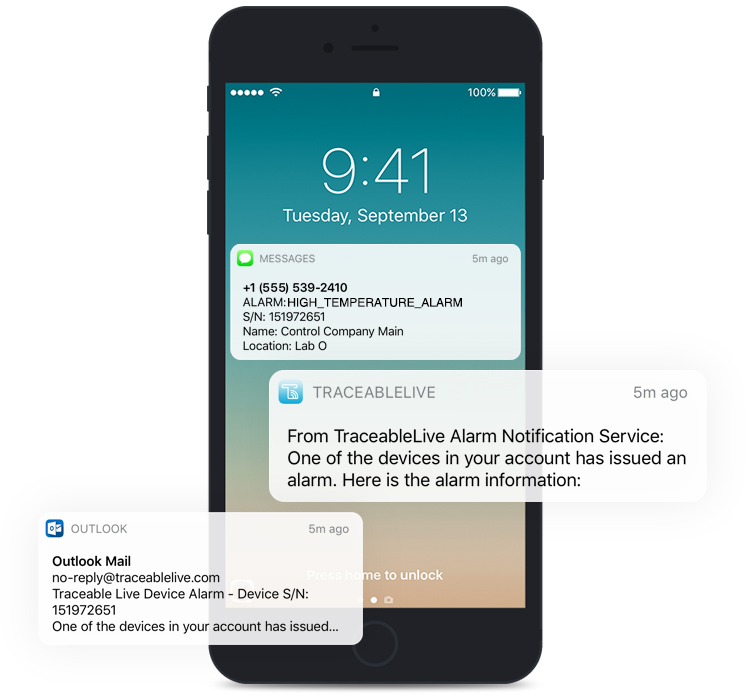
with Apple Watch, Voice call, mobile push, e-mail, and text notifications.

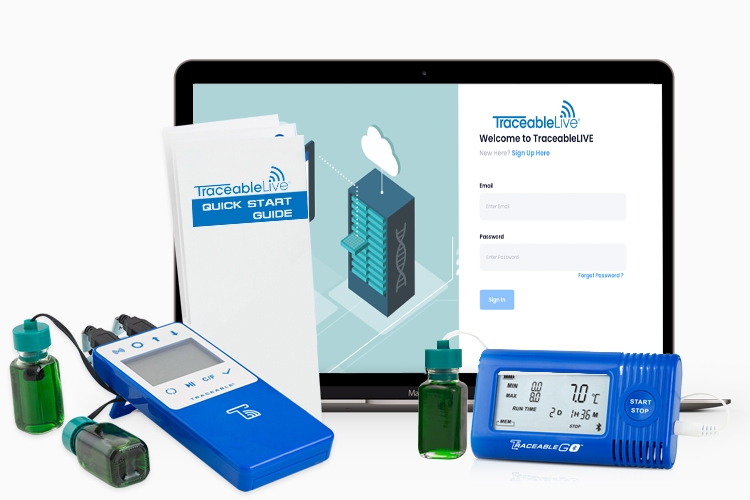
Reduce your Risk! Simplified Cloud Monitoring with TraceableLIVE®
We listened to your feedback and have added your most requested features to TraceableLIVE.
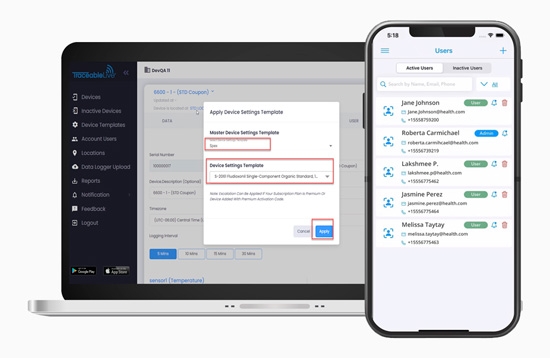
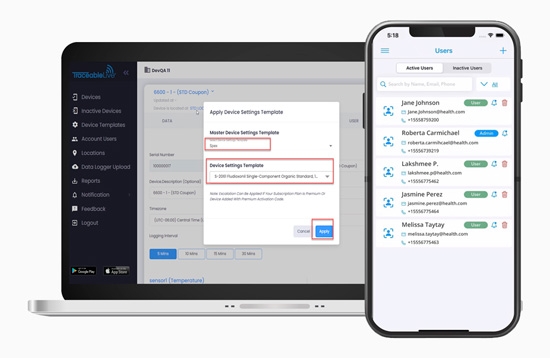
3 Updates now live: 1. Preloaded templates for even quicker setup. 2. Custom templates. 3. Device-based user notifications.
Get notified wherever you are—
it's all on your wrist!
Accessing your TraceableLIVE devices couldn’t be easier. TraceableLIVE paid subscribers will be able to access their devices and notifications via Apple Watch®.

TraceableLive® Subscription Plans
Stay in control of your subscription by adding as many or as few devices at any given time and your subscription amount will automatically adjust.
1 User Only
FREE
- E-mail and Push Alarms
- 1 Month Data Storage
- 1 User Only
- Up to 3 devices can be added to the account
- Calibration due and other notifications
Standard
$
100
per device / year
- E-mail and Push Alarms
- Preloaded templates included for Spex products and more
- Apple Watch compatibility
- No limit on devices that can be added to account (each device must have a subscription)
- Unlimited Users
- SMS Text Notifications*
- Monthly subscription available $8.99/Device with a credit card on traceablelive.com
Premium
$
165
per device / year
- Voice Call, E-mail and Push Alarms
- Preloaded templates included for Spex products and more
- Create unlimited custom alarm/settings templates
- SMS text notifications included
- Apple Watch compatibility
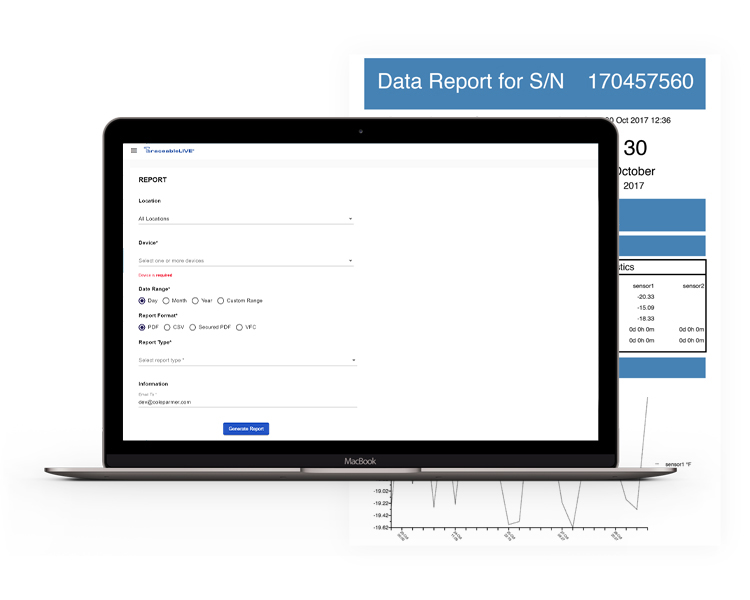
- Unlimited Data Storage
- No limit on devices that can be added to account (each device must have a subscription)
- Unlimited Users
- 21 CFR Part 11 compliance**
- Monthly subscription available $14.99/Device with a credit card on traceablelive.com
To purchase a plan, register or log in to traceablelive.com.
*SMS Text notification is available only on monthly credit card subscription add $2+/month/device or comes included in Premium.
**Meets 21 CFR Part 11 North American Compliance and Annex 11 for Europe.
TraceableLIVE® Fully Compliant Solution
Meets 21 CFR Part 11 North American compliance and Annex 11 for Europe. All devices include ISO 17025 accredited calibration.
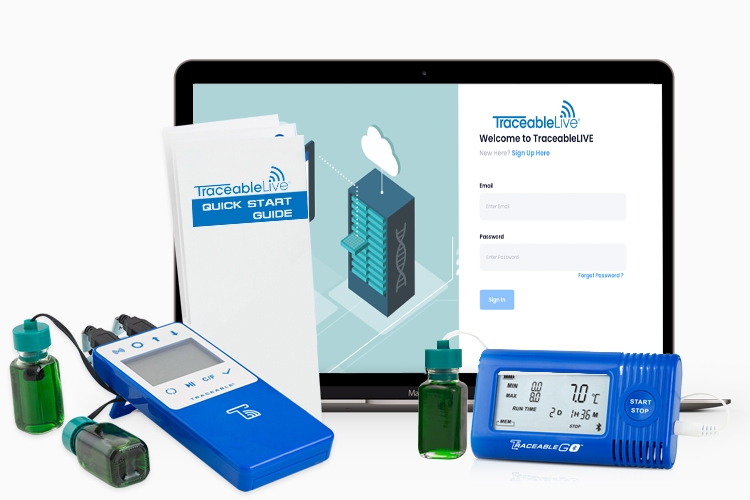
View accreditationsSimple to Set Up
Purchase Data Logger. Download App. Scan QR Code. Start Monitoring.
Download Set up Guide